with the development of internet technology, the network stability and performance of data centers have become important considerations for enterprises when choosing service providers. as a key data exchange node, the bgp computer room in shatin, hong kong carries a large number of data transmission tasks. this article will delve into the network stability and performance evaluation of the bgp computer room in sha tin, hong kong, to help readers better understand the advantages and challenges of this important infrastructure.
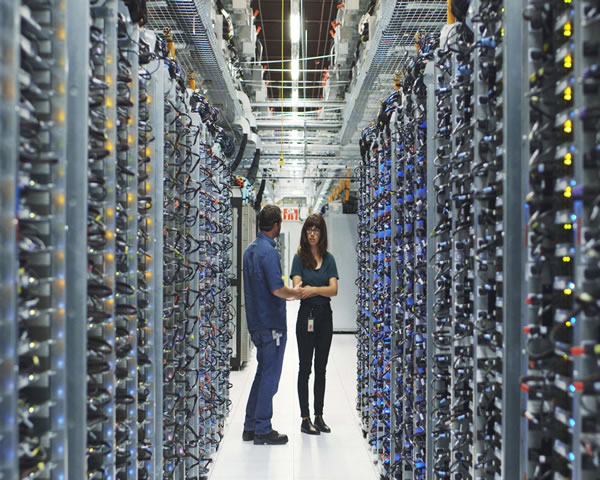
the bgp computer room in shatin, hong kong is located in a strategic geographical location in hong kong and has excellent network connection conditions. bgp (border gateway protocol) is the main routing protocol in the internet, ensuring efficient data transfer between different autonomous systems. the computer room not only provides high-bandwidth solutions, but also has multiple redundant lines to ensure high network availability. by analyzing the architecture and technical configuration of the shatin bgp computer room, we can better understand its important impact on network stability.
network stability refers to the reliability and consistency of the network under normal operating conditions. the network stability of the shatin bgp computer room is mainly affected by the following factors: first, the quality of the hardware facilities. modern routers and switches can effectively reduce the failure rate. second is the network topology. a reasonable architecture can avoid single points of failure and achieve load balancing. in addition, the power redundancy and environmental monitoring system in the computer room are also important guarantees for ensuring long-term stable operation of the network.
when evaluating the performance of the bgp computer room in shatin, hong kong, we mainly focus on the following criteria: latency, bandwidth, packet loss rate and throughput. latency refers to the time it takes for data to reach its destination from the source. low latency can improve user experience; bandwidth refers to the amount of data that can be transmitted per unit time, which directly affects the efficiency of data transmission; packet loss rate reflects the reliability of the network, and high packet loss rate will lead to unstable data transmission; finally, throughput is a measure of the actual data transmission rate and is also an important indicator for evaluating network performance.
the bgp computer room in shatin, hong kong has many advantages in terms of network stability and performance. first, the location of the computer room enables high-speed connections to major global networks. secondly, the flexibility of the bgp protocol allows data traffic to be automatically adjusted to ensure network load balancing. however, as user demands continue to increase, computer rooms are also facing challenges of insufficient bandwidth and network congestion. in this regard, network operators need to conduct regular performance evaluation and upgrades to cope with future traffic growth.
with the rise of cloud computing and big data, the network stability and performance of data centers will become increasingly important. in the future development of the bgp computer room in shatin, hong kong, it is necessary to focus on continuous technological innovation, such as the introduction of artificial intelligence technology for network monitoring and fault prediction. in addition, with the popularization of 5g technology, computer rooms also need to consider how to be compatible with emerging technologies to improve overall network performance and user experience.
by evaluating the network stability and performance of the bgp computer room in shatin, hong kong, we can see that it has significant advantages in data transmission and service quality. however, as network demands continue to grow, computer rooms are also facing many challenges. it is recommended that operators conduct regular network performance tests and optimize network architecture in a timely manner to ensure that high-quality network services can be maintained under high load conditions. in addition, exploring the application of new technologies will provide more possibilities for future network development.

- Latest articles
- Analysis Of Server Matching Mechanism And Delay Optimization Suggestions For Playerunknown’s Battlegrounds Japan
- How To Apply Singapore Server Speed Reading In Content Distribution Scenarios
- How To Judge Whether The 20 Yuan Us High-defense Cloud Server Meets The Protection Needs Of Short-term Activities
- Initial Security Reinforcement And Protection Configuration Guide After Installing The Us Vps System
- Explanation Of Environmental Pollution And Cleanup Standards For Fires In Thailand's Washing Machine Rooms That Concern The Public
- Hong Kong Vps Uses Ccproxy To Implement Traffic Control And Access Auditing In An Enterprise Scenario
- Technology Comparison: Delay And Cost Analysis Of Taiwan Ip Server Cloud Space And Dedicated Line Access
- Interpretation Of The Meaning Of Tencent Servers In Vietnam For Wechat And Tencent Cloud Service Access
- Interpretation Of The Meaning Of Tencent Servers In Vietnam For Wechat And Tencent Cloud Service Access
- Market Trends Shown In The German Tractor And Rv Price List And Analysis Of Second-hand Car Value Preservation
- Popular tags
-
How To Choose A Suitable Do Hong Kong Computer Room To Improve Business Efficiency
how to choose a suitable do hong kong computer room to improve business efficiency and explore computer room selection factors and best practices. -
Advantages And User Experience Evaluation Of Xiaoniao Cloud Hong Kong Server
this article discusses the advantages and user experience evaluation of xiaoniao cloud hong kong server to help users choose the appropriate cloud server. -
Security Protection: Hong Kong Station Group’s Self-operated Computer Rooms Use Technical Means To Deal With Ddos Attacks
this article systematically introduces the technical means of protecting the self-operated computer rooms of the hong kong station group in response to ddos attacks, including practical strategies such as network redundancy, traffic cleaning, bgp anycast, rate limiting, application layer protection and emergency response.